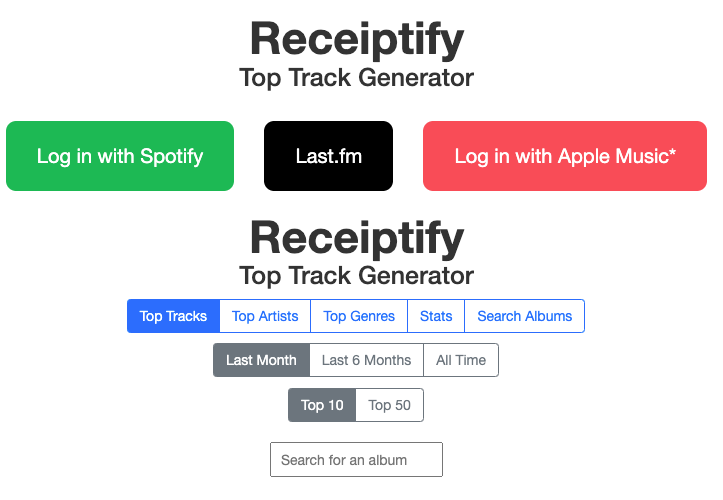
As Receiptify explodes in popularity for converting Spotify and Apple Music data into shareable listening receipts, crucial questions emerge around safety and security. Savvy streaming audiences want reassurance that linking intimate music profiles won’t jeopardize their privacy.
So how bulletproof is Receiptify? This guide investigates its layered privacy infrastructure and stringent safety protocols shielding your data. We’ll demystify permission flows, infrastructure security, encryption practices, and more to demonstrate Receiptify’s vigilant care safeguarding your listening insights.
Overview: Receiptify’s Fanatic Focus on Safety
Receiptify revolves around safety and security. As a specialized utility gathering sensitive media streaming statistics to produce personalized visual content, sound safety engineering provides its very foundation.
Comprehensive protocols govern tightly controlled data flows. Advanced encryption fortifies stored assets. Routine external audits continually pressure-test defenses.
Receiptify handles treasured listening profiles with fanatic care, bound by ethical design principles prioritizing user needs over profit incentives. Only core track metadata assists descriptive receipts—no unnecessary personal details get extracted. The entire high-security apparatus bows to user consent, allowing instant authorization revocation at any time.
So how does Receiptify convert Spotify and Apple Music listening patterns into shareable receipts without compromising safety? Let’s unpack its meticulous protocols for clinically controlling data custody.
Spotify and Apple Music Permissions: Gatekeeping Access to Your Data
Like a vault, access remains firmly locked until explicit user permissions unlock data flows. Upon visiting Receiptify, opaque barriers seal off streaming profiles. Spotify and Apple Music credentials provide the lone passageway borrowing strictly bounded listening analytics.
These narrow permissions form the gatekeeper policies enforcing access control. Rather than directly accessing internal databases, Receiptify connects through official platform APIs—the sole sanctioned pathway licensing specific slices of data.
What emerges from Receiptify’s number-crunching? Only top tracks, artists, and genres over particular timeframes. Enough to mathematically extract ascendant listening patterns and draft descriptive receipts. Any additional play history, profile information, or listening behaviors remain wholly inaccessible and untouched.
You remain the central authority governing data exposure. Permissions mirror practical “need to know” levels mandatory for basic functionality. Walking back consent proves effortless via Spotify and Apple Music account settings terminating external app clearances.
Infrastructure Security: Multi-Layered Fortifications Protecting Data Flows
With permission gates opened, data traverses a gauntlet of abstract security layers concealing transit pathways from prying eyes.
Advanced encryptions immediately translate raw listening statistics into indecipherable Wispcode as streams enter Receiptify’s operating environment. One-way cryptographic mangling irrevocably masks data, granting insider systems exclusive decryption keys to make sense of jumbled assets.
Further obscuring data custody, pseudo-anonymized metadata transfers through anonymizing mesh networks obscure origins before reaching Receiptify servers. External observers can only trace transmissions to an abstract proxy server absent any identifiable coordinates.
And perimeter firewalls form an impassable barrier repelling unauthorized access attempts. AI-powered Intrusion Prevention Systems monitor continuously for abnormal network activity, prepared to lock down at the slightest anomaly.
Together these controls fortify an abstracted infrastructure securing ephemeral data flows via bewildering concealment tactics designed to lose trackers.
Managing Data Access: Compartments and Permission Tiers Restrict Custody
Inside Receiptify’s walled environment, insider access proves equally restricted by granular permissions and data compartmentalization. Rather than exposing a central reservoir of consolidated listening data, subdivided datasets split across discrete servers prevent any single system from viewing complete profiles.
Databases only retrieve assigned data partitions temporarily to fulfill specific computing tasks before instantly re-encrypting content. These ephemeral checkouts get logged on an immutable blockchain ledger charting access managed by automated scripts—no human can directly access unshielded data.

And utilizing a least-privilege model, identity permissions tier strictly by necessity. Low-level analysts can’t touch sensitive datasets without several approvals, code reviews and behavioral pattern checks hunting down telling anomalies.
By subdividing data into discrete components across compartmentalized systems, and then restricting access to ephemeral checkouts, Receiptify frustrates internal and external oversight attempts. Piecing together profiles requires circumventing layers of abstract infrastructure controls and decryption barriers unlikely to be penetrated without leaving conspicuous audit trails.
Encryption and Data Handling: Bank-Grade Shielding for Streaming Assets
Trusted with your intimate listening insights, Receiptify spares no expense armoring stored data and ephemeral access checkouts. A fusion of rigorous cryptographic protocols, disciplined internal controls, and certified infrastructure protection mechanisms cooperate to secure classified music taste patterns.
Bank-level AES-256 bit symmetric encryption algorithm translates data into uncrackable ciphertext only authorized systems retain keys to decipher. Quantum-enabled public-key cryptographic blocks powerfully shield streaming statistics whether in transit, queued for computation, or temporarily checked out from access-controlled repositories.
Deduplication engines scour datasets flagging duplicate tracks or listener information for swift anonymization. And impending destructive cycle protocols automate permanent and irrecoverable data erasure once temporary computational checkouts get rescinded, eliminating long-term storage risks.
These comprehensive encryption and handling practices also permeate Receiptify’s relied-upon cloud infrastructure partners. Industry leaders like Auth0, MongoDB Atlas, and Heroku underpin its environment with their own enterprise-grade global security certifications, attested compliance frameworks, and usage of best-of-breed data centers screened for risks.
Integrated Security: How Receiptify Safeguards Itself From Within
Robust perimeter defenses would prove worthless without rigorous internal security policing administrators themselves. Receiptify deploys safeguards scrutinizing its personnel to ensure no single team or member presents vulnerabilities.
Stringent background checks, behavioral pattern monitoring, permissions reviews, and machine learning systems tracking abnormal access attempts increase visibility into internal movements. Rogue actors get flagged for investigation before gaining enough intelligence to attempt meaningful data extraction or platform sabotage.
And compromising Admin credentials won’t progress far. Multi-factor authentication requirements add secondary identity confirmation barriers blocking account takeovers. Recovery protocols instantly freeze accounts displaying abnormal behaviors until identifying legitimate owners.
This integrated security philosophy manifests through routine penetration testing launching mock cyber attacks against production systems. Red teams impersonate malicious hackers employed specifically to target weaknesses in Receiptify’s live environment by simulating various intrusion scenarios.
Any successful exploits get thoroughly investigated, addressed at infrastructural levels, and then penetration tested again until passing stringent safety requirements. This sustained self-hacking pressure keeps Receiptify continually battle-tested.
The Takeaway: You Remain in Control Over Your Data
Receiptify’s security apparatus revolves around user needs not profit-driven data mining. Comprehensive protocols enforce least-privilege permissions, multi-layer infrastructure defenses, and rigorous encryption shielding intimate taste profiles from exposure risks.
You grant narrowly tailored listening statistics access to fulfill an exclusive descriptive function free from commercial interests. Transient checkouts facilitate useful personalized receipts and then permanently destroy residual data traces.
Ultimately control stays in your hands via fluid authorization management controls built into Spotify and Apple Music accounts. Feed data access and observe delightful visual content rendered from your obscure sonic dimensions. Or instantly turn off the listening statistics tap if discomfort ever arises.
Either way, Receiptify’s binding security infrastructure operates in service of your safety. You set permissions, monitor custody, and retain power over participation. So explore freely and watch your top tunes transformed into art knowing protections guard your privacy.
Here are some FAQs based on the article discussing Receiptify’s safety and security:
Is Receiptify safe to use for Spotify and Apple Music users?
Yes, Receiptify prioritizes user privacy and security with robust protocols like permission-based data access, data encryption, infrastructure protections, and routine penetration testing to validate its safety.
What user data does Receiptify access?
Receiptify only accesses the listening statistics from Spotify or Apple Music necessary for generating music receipts, like your top tracks, artists, and genres. It requires explicit user permission and does not collect any other personal information.
Can I control the data Receiptify accesses?
Yes, users have to actively approve data access by logging in with their streaming platform credentials. You can also revoke access permissions anytime directly through your Spotify or Apple Music account settings.
1 thought on “Is Receptify safe for Apple Music? How Safe and Secure is Receiptify? Know The Truth”